The Internet’s Scary Future: New Technology Threats
While the internet has undoubtedly brought new benefits, it’s also brought new problems, as cyber criminals look to exploit our ever-growing reliance on connectivity.

The internet has provided malicious hackers with a variety of new ways to make money and cause disruption.
Cyber criminals use phishing emails, malware, ransomware, and other malicious tactics to steal bank details, passwords and other personal information.
We’re yet to fully secure networks against today’s internet threats, yet technology continues to evolve at a rapid rate, bringing new threats that we must be made aware of to prepare and defend against them.
New Technology Threats:
1. Quantum Computing: Crypto-jacking & Crypto-mining
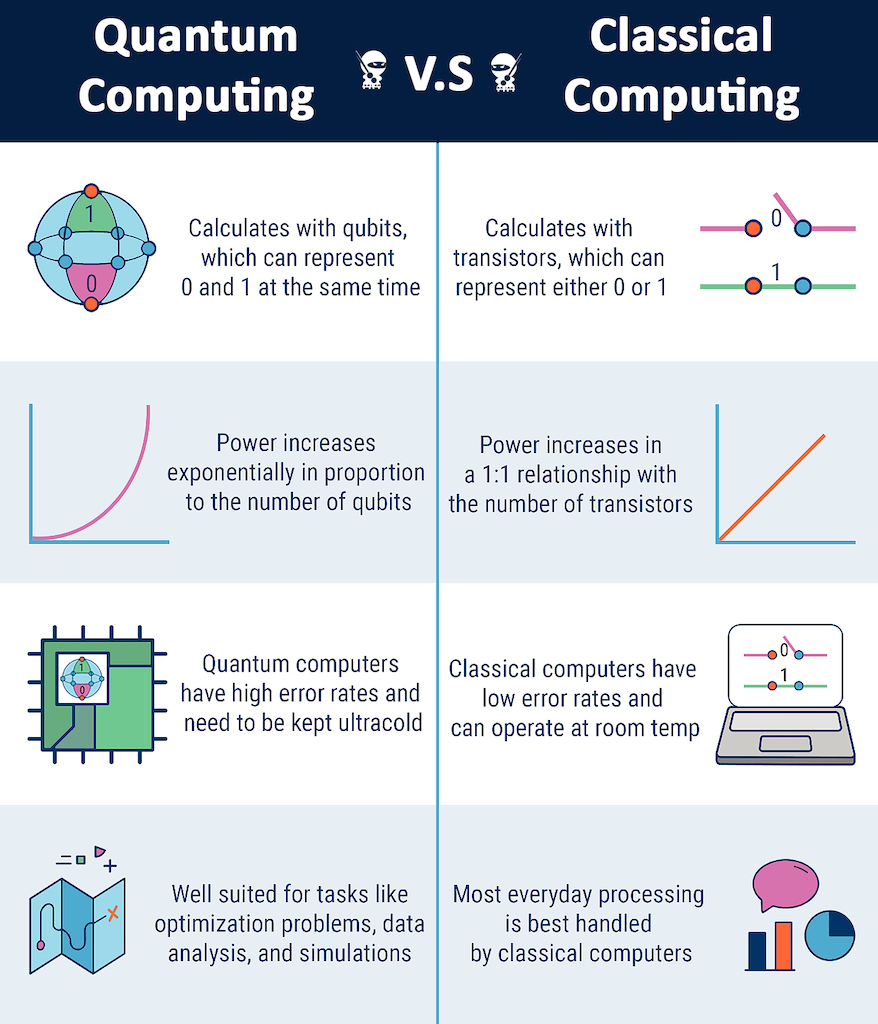
One of the most significant technological breakthroughs heading our way is quantum computing, which promises to quickly solve complex problems that classical computers cannot.
While this advance will bring benefits to scientific research and society, it will also create new challenges. The power of quantum computing could make quick work for attackers to crack the encryption algorithms we’ve used for decades to secure a range of areas, including online banking, secure communications, and digital signatures.
“What was an entirely appropriate encryption key length 20 years ago is no longer appropriate.”says Martin Lee, technical lead of security research at Cisco Talos.
Currently, quantum computing is expensive and the expertise required to develop it is restricted to large technology companies, research institutions and governments.
However, like any innovative technology, it will eventually become more commercially available and easier to access, and cyber criminals will be looking to take advantage of quantum.
The US Cybersecurity and Infrastructure Security Agency (CISA) has already warned that action must be taken now to help protect networks from cyberattacks powered by quantum computing, particularly those that support critical national infrastructure.
While disruptive cyberattacks powered by quantum computing are a key cybersecurity threat of the future, quantum computers could themselves be a lucrative target of hackers.
One specific attack example is crypto-mining malware. This form of malware is installed on computers and servers to secretly use the power of someone else’s network to mine for cryptocurrency and pocket the profits, all without needing to pay for the resources or the power being consumed.
Cryptocurrencies, such as Bitcoin, are generated by computers by solving complex mathematical problems, the sort of mathematical problems that could be relatively trivial for a network of quantum computers to solve.
That means that if cyber criminals were able to plant crypto-mining malware on quantum computers, they could get very rich very quickly, and at almost no cost to themselves.
Infecting a quantum computer would allow somebody to start calculating very complex algorithms. A crypto miner on a quantum computer, is going to tremendously speed up mining capabilities, and those things becoming a target of trivial cyberattacks.
2. Exploiting Artificial Intelligence & Machine Learning
Quantum computing isn’t the only emerging technology that cyber criminals are looking to take advantage of, we can also expect them to exploit developments in artificial intelligence (AI) and machine learning (ML).
Similar to quantum computing, AI and ML look set to power innovations in a range of areas, including robotics and driverless cars, speech and language recognition, healthcare and more.
AI that can adapt and learn can be used for good, but ultimately, once it becomes more widely available, it’s only a matter of time before cyber criminals are using it to help make cyberattacks more effective.
Mikko Hyppönen, chief research officer at WithSecure states, “We will start seeing malware campaigns, ransomware operations and phishing campaigns being run totally automated by machine-learning frameworks. It hasn’t been done yet but it wouldn’t be very hard at all to do.”
One means of exploiting this technology would be programming a text-based generation algorithm to send out, and reply to, common spam emails or business email compromise (BEC) campaigns.
Rather than needing a human to take time out to write and reply to messages, criminals could rely on an algorithm that can also analyse which responses are most likely to be real victims that are worth replying to, rather than people who see through the spammers lures.
That reality means in future you could end up being scammed, by a bot.
There’s also the potential that cyber criminals could use advancements in ML to develop self-programming smart malware which.
Rather than needing a developer to support it, this malware could update itself by automatically reacting to the cyber defences it meets to have the greatest chance of being effective.
When self-programming programs become more capable, it could change the code, to make it more complex to understand, make it so it’s different every time, and it could try to create undetectable versions.
All of that is technically doable, we simply haven’t seen it yet, and unfortunately it’s predicted we will.
3. Deepfakes
AI being abused to power cyber threats isn’t a just a future problem for the internet, it’s already happening now, with deep learning being used to power deepfakes, which are videos that look like they’re real people or events but are actually fake.
They’ve been used in political misinformation campaigns, pranks to fool politicians, and they’re already being used to enhance BEC and other fraud attacks, with criminals using deepfake audio to convince employees to authorise significant financial transfers to accounts owned by the attackers.
“We’re entering this brave new world around deepfake video that will be used to commit crimes. Not just manipulation, but also in disinformation and misinformation,” says Theresa Payton, CEO of Fortalice Solutions and former CIO at the White House.
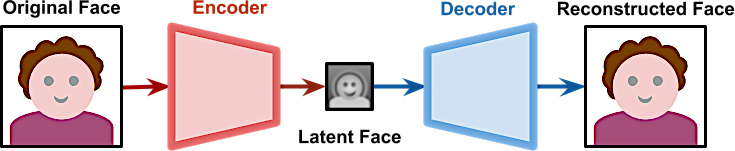
Take the example of CEOs who are in the public-facing realm. They appear on television, they give speeches, are there are videos of them online, so it’s relatively simple to find recordings of what they sound like. Scammers will use those resources through deepfake technology to mimic their voice.
After all, if an employee gets a call from the head of the company telling them to do something, they’re likely to do it, and the cyber criminals behind these attacks know this fact.
There are known cases where deepfake audio was used to successfully convince somebody to transfer money to a place they shouldn’t have transferred it.
As the technology behind deepfakes continues to improve, it means that it will only get harder to tell what’s real from what’s fake.
4. Internet Of Compromised Things
Deepfakes aren’t the only area where cyber threats could impact our everyday lives if the future of the internet isn’t secured properly.
Increasingly, smart Internet of Things (IoT) devices are becoming a bigger part of our daily existence, with a variety of sensors, appliances, wearable devices and other connected products appearing in homes, offices, factories, and more.
While there are certain advantages to connecting IoT devices to our home and workplace networks, this increased level of networking is also creating a larger attack surface for cyber criminals to try to exploit.
“When you add functionality and connectivity into everyday devices, they become hackable. Devices that were unhackable become hackable. It might be very hard. Nevertheless, it is always doable. There is no secure computer. There is no unhackable device,” explains Hyppönen.
“This is the thing that’s happening now during our time, and there’s no stopping it. It doesn’t matter what we think about it, it’s going to happen anyway, and it’s going to be increasingly invisible.”
Think about your home appliances: it’s increasingly likely they’re ‘smart’ and connected to the internet. Anything from your television to your toothbrush could now be internet-connected.
For appliance manufacturers, building internet-connected devices is a relatively new phenomenon. Some vendors might not even think aboutcybersecurity threats in the design process at all, leaving their products vulnerable to hackers.
While hackers coming after your coffee machine or your fish tank might not sound like a concern, it’s a point on the network that can be accessed and used as a gateway to attack more important devices and sensitive data.
The other problem to consider is there’s already millions and millions of IoT devices out there that lack security – and might not even be supported with security updates.
Think about how many smartphones can’t receive security updates after just a few years. Then scale that reality up to the fast-growing IoT, what’s going to happen if devices that aren’t regularly replaced?
There’s no software vendor on the planet that would support software written 20 years ago. It’s suggested that when manufacturers no longer support updates for their devices, they should open source it to allow others to do so.
You would get the security patches for your old, outdated legacy things by paying for the service just like you pay for any other service.
Connected devices are already becoming ubiquitous throughout society, with no sign of this trend slowing down – whole smart cities will become the norm.
However, if cybersecurity and compliance isn’t a key force driving this trend, it could lead to negative consequences for everyone. Attacks will happen at a scale and speed you’ve never seen before, and that is incredibly concerning.
5. Cyber Security Threats
Despite the potential threats on the horizon, there’s still an optimistic view about the future of the internet.
While cyber criminals are going to be using new technologies to help improve their attacks, those responsible for defending networks will also be deploying the same technologies to help prevent attacks.
Cybersecurity experts are continuing to model nefarious behaviors, then use artificial intelligence, big data, analytics, and different types of machine learning algorithms to continue to refine technology.
Now, will it block everything? No, because cyber criminals are always adapting their tactics, but their optimistic that they will be able to block more of the basic-to-medium types of threats that still need more remedies today.
Cybersecurity is improving overall and even with new technologies on the horizon, it doesn’t mean cyber criminals and other malicious hackers will simply have it easy.
“Computer security has never been in better shape than today. That’s a controversial comment – people on the street would most likely think that data security has never been worse because they only see the failures. They only see the headlines about yet another hack,” he says.
The fact is, if you compare the cyber security of our computers today and a decade ago, it’s like night and day. We’re getting much, much better at security, making it much harder for attackers to break through.
Let’s hope that situation remains the case, the future stability of the internet depends on it being true.