A Guide to the Various Types of Malware
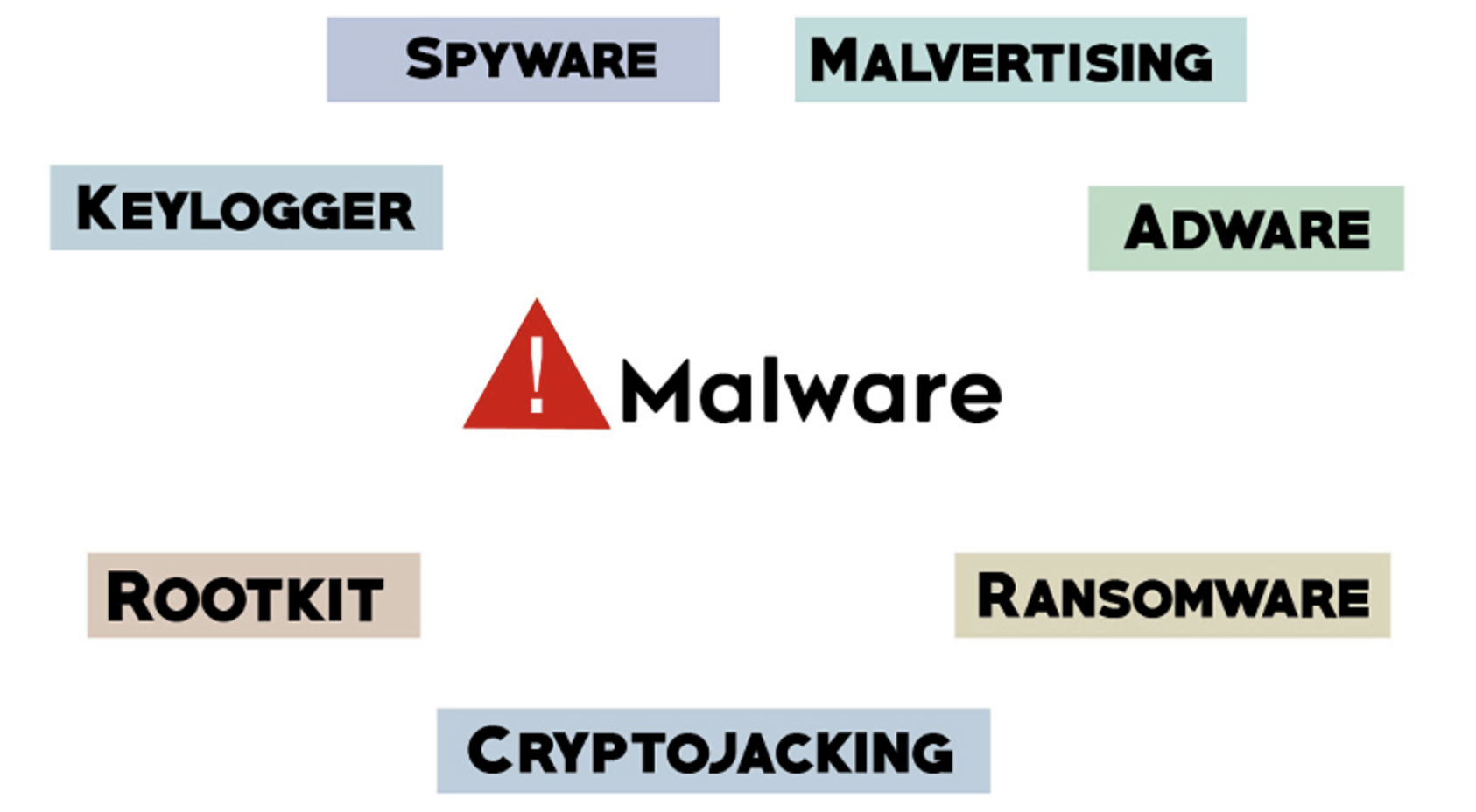
Malware typically refers to malicious software comprised of worms, viruses, Trojans, and several other harmful programs. Hackers and spammers use Malware to damage your data and gain access to your confidential and sensitive information. While no device is immune to malicious software or infections there are effective security practices you can implement to help prevent an attack from happening. Many companies utilize our Ethical Hacking and Security Services to assist in finding any security vulnerabilities in your system. This service helps make your systems more reliable as well as, secure your commercial and personal data. It is also crucial to understand the different types of malware and how to detect and prevent it. Malware is generally put into categories depending on how fast it spreads. Hackers often use worm, virus, and Trojan interchangeably, however, the three forms are subtly different when infecting the systems:
1. A virus is a form of computer code that has the ability to insert itself within other standalone program’s code. It not only leads the program to perform malicious activities but also spreads quickly.
2. A worm is also malicious software that spreads itself by reproducing itself. It can infect multiple devices at the same time.
3. Trojan doesn’t reproduce like a worm and virus, but it can trick users into something they are looking for. Once clicked, the Malware activates, damages the system, and spreads quickly.
Attackers and hackers can also install the virus manually on devices and computers if they gain physical access to the system or use privilege escalation for remote administrator control. This is sometimes more harmful than the automatic codes and programs infecting your computers. Here is a breakdown of some of the most common manually installed Malware your computer may have:
1. Spyware: Usually the most unsuspecting users become the victim of “Spyware.” A hacker installs spyware onto the system to secretly collect the data. Typically, it has a purpose to spy on activities you do on your computer or other devices. It gathers the data you exchange with your peers and sends the information to a third party.
2. Keylogger: If a hacker steals your password using Malware, they might use a “keylogger,” which is specific spyware. It can record the keystrokes to copy the details of your password.
3. Rootkit: A rootkit is a manually installed Malware that can shift the remote access and control from one computer to another. This Malware is defined as a set of software tools that can gain root access, such as administrative level control over the other system and the presence.
4. Adware: This malware redirects the ads on the web by forcing the browser. It further leads the users to download various ads that have more viruses and malicious software. This software usually tempts users with free games, browser extensions, and programs.
5. Ransomware: This encrypts the files in the hard drive. The attacker usually demands a large sum of money in exchange for the system’s description key. If you don’t access your description key, it is mathematically challenging to regain access to your data and files.
6. Cryptojacking: This is defined as crypto mining malicious software that infects computers and uses them to mine Bitcoin. An attacker runs this mining software in the background on the system or in the browser window without you knowing.
7. Malvertising: This malware type uses legitimate ads to infect the computers. For instance, a cybercriminal pays to run an ad on an authentic website, and when you click on the ad, it redirects you to a malicious site. It may also install various Malware and virus on your computer. Sometimes, the malicious software executes itself automatically without having you click anything. This is a drive-by download.
How can you detect and prevent Malware? Phishing emails are one of the primary reasons for malware infections on computers. It is crucial to make sure that you lock down your email system tightly, carefully check all the attached documents and restrict behavior. You can also take some technical measures to protect your system such as patching, updating, and performing vulnerability assessments on your digital infrastructure. Use hi-tech visibility tools to detect unfamiliar activities on your network since they can help you detect malicious software and indicate if there is a malware infection. Malware removal can be very challenging and the methods may vary depending on the type of malware that has infected your computer. It is always better to consult pros like us to help you recover from malicious software attack.








Business phone reverse lookup
October 14, 2023Your passion for this subject is admirable.