A stealthy new form of malware is targeting Linux systems in attacks that can take full control of infected devices, and use this access to install crypto-mining malware. This malware has been detailed by cybersecurity researchers at AT&T Alien Labs, they call it Shikitega. This malware targets endpoints and Internet of Things devices that run on Linux operating […]
Targets of ransomware rarely publicly acknowledge attacks. More openness would help everyone. Ransomware is one of the most significant cybersecurity issues we face, as cyber criminals hack into businesses, schools, hospitals, critical infrastructure and more, in order to encrypt files and demand a ransom payment for the decryption key. Despite warnings not to, many victims pay […]
Google Chrome users on Windows, Mac, and Linux need to install the latest update to the browser to protect themselves from a serious security vulnerability that hackers are actively exploiting. “Google is aware of reports that an exploit for CVE-2022-3075 exists in the wild,” the company said in a September 2nd blog post. An anonymous tipster reported […]
Keeping on top of cybersecurity risks is a constant challenge. Threats including phishing, malware and ransomware are continually evolving and adapting, as cyber criminals regularly find new, innovative ways to conduct malicious hacking campaigns, break into computer systems and find a way to stay there. Many companies are having difficulties keeping up with the technological world and threats that come with […]
Cyber attackers regularly exploit unpatched software vulnerabilities, but they continuously target security misconfigurations to gain initial access into victims systems. The US Cybersecurity and Infrastructure Security Agency (CISA), FBI and NSA, as well as cybersecurity authorities from Canada, New Zealand, the Netherlands, and the UK, have created a to-do list for defenders in today’s heightened […]
In todays world data breaches happen on a daily basis, involving everything from device theft to vulnerability exploitation and open AWS buckets exposed for the world to see. Businesses and home users alike must educate themselves and employ encryption software to protect their personal, business, and critical data that they may be legally liable for […]
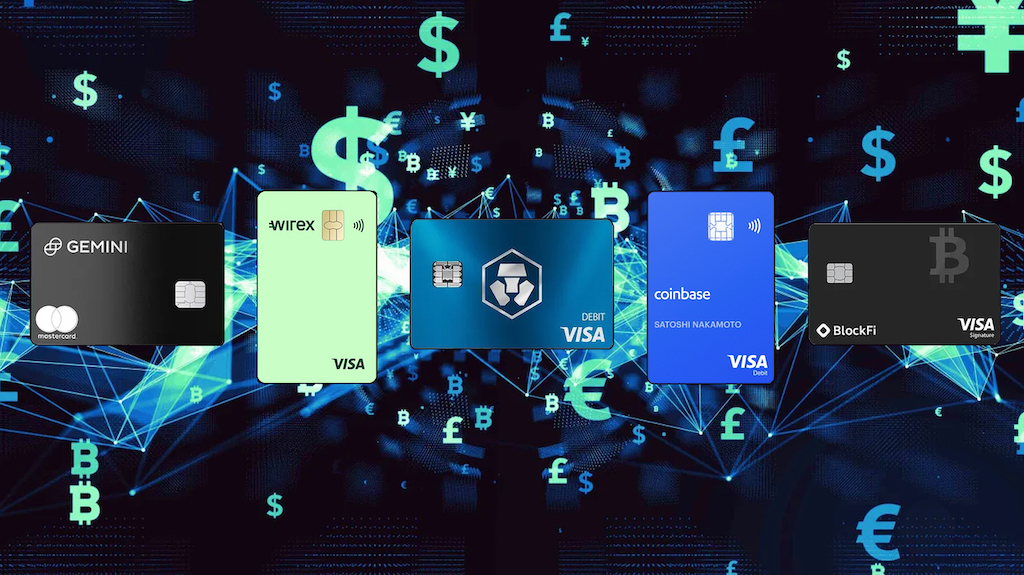
Increasingly, the world is going digital, and that includes how we spend. The cryptocurrency space is quickly evolving, with many new trends and products coming about. One new trend that is quickly gaining in popularity is the crypto rewards credit card. As more and more crypto cards are becoming available, consumer interest is growing to earn […]
While robust passwords go a long way to securing your valuable online accounts, hardware-based two-factor authentication takes that security to the next level. Password policy compliance is important, and a crucial step to securing your online life. Some of your online accounts for example, Google Account or Dropbox, might be so important and contain such […]
According to analysis by cybersecurity researchers, over half of ransomware attacks are targeting one of three industries; banking, utilities and retail but they’ve warned that all industries are at risk from attacks and no business or industry is safe. This data was gathered during a period when some of the most high-profile ransomware attacks of the past […]