To protect your cell phone from malicious programs, you can use several strategies:
Whether it’s macOS for desktops and laptops or iOS for mobile devices, involves several key steps. Here’s a general guide to help you enhance the security of your Apple devices:
It’s no secret that there are many dangers when protecting online accounts with only basic password-based authentication. Despite this, the transition to stronger forms of authentication has been slow. As consumers and businesses become wiser to the imperative of better protecting their accounts, they realize that two- and multi-factor authentication is a must have. The National Cyber Security Centre (NCSC) recommends 2FA for all […]
Discover The system is shutting down. There is no way of stopping it, and now your software has been attacked, hacked, and manipulated in a way that is just too late. Hackers are attacking through the software supply chain, and cloud security is now considered as a top priority. Although cloud-computing services are viewed as […]
Cybercriminals have been targeting more and more Mac users recently and by taking the proper actions, you can fully safeguard your Mac against attacks. Cybersecurity doesn’t have to be complicated, you can easily protect your Mac and your most sensitive data in a few simple steps. Macs do have built-in security settings, but they’re often not used effectively leaving your […]
Exploiting security flaws is one of the major tactics used by cybercriminals to attack organizations. Vulnerabilities are an unfortunate fact of life for operating systems, applications, hardware devices and databases. An attack against a database can easily compromise sensitive and confidential user and customer data. Based on analysis fromImperva covering 27,000 on-premises databases around the […]
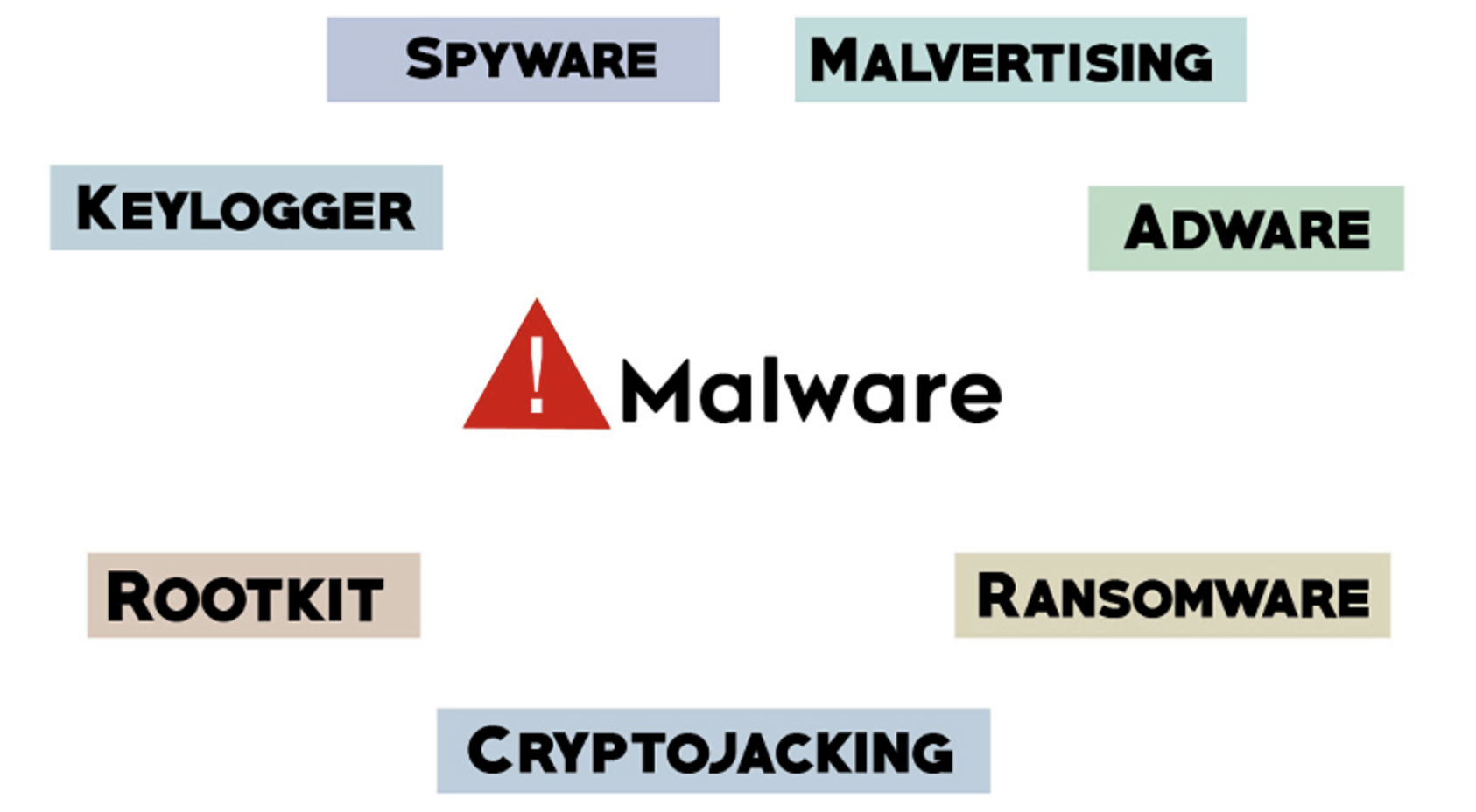
Malware typically refers to malicious software comprised of worms, viruses, Trojans, and several other harmful programs. Hackers and spammers use Malware to damage your data and gain access to your confidential and sensitive information. While no device is immune to malicious software or infections there are effective security practices you can implement to help prevent […]
Security vulnerabilities in millions of Internet of Things (IoT) devices, including connected security cameras, smart baby monitors and other digital video recording equipment, could allow cyber attackers to compromise devices remotely, allowing them to watch and listen to live feeds, as well as compromise credentials to prepare the ground for further attacks. The vulnerabilities in IoT devices that use […]
Preparing and approving the cybersecurity budget is an important responsibility for IT security executives. The budget has a direct impact on the organization’s ability to avoid or overcome cyberattacks. If the cybersecurity budget fails to cover all key bases, the organization could be forced to spend more on recovering from the cyberattack. While the obvious cybersecurity expenses […]
- 1
- 2