10 Anti-Fraud Measures To Secure Your Business & Customers
In today’s digital landscape, no business is safe from fraud, learn how to fight back against cyber criminals and better protect your valuable information.

Today’s cyber criminals target everyone and everything, from giant global corporations to the smallest mom-and-pop shops.
Keeping on top of cybersecurity risks is a constant challenge. Cyber crime is rapidly evolving, making cyber security essential for every business, no matter the industry.
Many companies are having difficulties keeping up with the technological world and threats that come with it, resulting in security holes in networks and vulnerabilities left unpatched.
10 Anti-Fraud Measures:
1. Keep On Top Of The Latest Fraud Trends
Education is the best prevention. This is particularly true in the world of online fraud, where new attack techniques pop up on a regular basis.
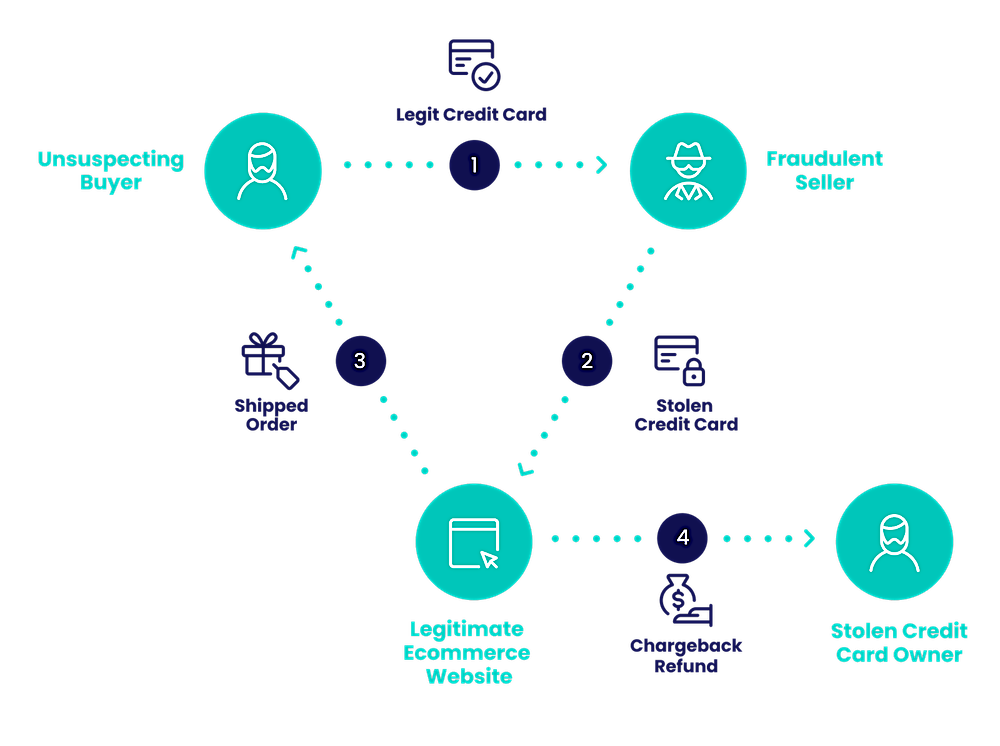
For instance, do you know how criminals use triangulation fraud to target online stores, increasing merchants’ chargeback rates and eating into profits?
- Pro tip: Follow risk experts on social media, read industry websites, like our bva IT blogs for useful resources and to stay onto of all things tech!
2. Identify Your Fraud Risk
No two online businesses are the same, which means fraudsters could attack you in very different ways. For instance, BNPL fraud is nothing like iGaming fraud.
The key is to anticipate the kind of risk you may face, whether you’re established or launching a new business venture, and have proactive measures in place to defend against cyber attacks.
- Pro tip: Run through all the steps in SEON’s risk assessment checklist to help you identify potential attacks on your company and check out the blog below to enhance your overall cyber security.
3. Invest In IT Security & Cyber Security Awareness Training
Fraud and cybersecurity sometimes overlap when it comes to IT security. You want to protect your user accounts but also ensure that your internal data isn’t compromised.
This isn’t something a lot of business owners want to hear, but risk management shouldn’t be an afterthought.
In fact, when done right, it can be a competitive advantage. You are essentially future-proofing your company from bad consequences such as:
- Revenue fluctuations
- Stalling of growth
- Loss of customer trust
- Bad business reputation
- Negative press and PR
It’s been shown that a single data leak, for instance, can cause stock prices to plummet by as much as 7.5%.
This can be a result of an account takeover, or hacking, but not matter the attack method, the results are equally detrimental.
- Pro tip: Set a dedicated budget for risk management, fraud prevention, and IT security training as soon as possible. Without the proper information technology operations and contingency plans in place, you could be left to deal with catastrophic consequences.
4. Educate Users About The Value Of Their Accounts
Cyber threats can come from any level of your organization. Workplaces must include cyber security awareness training to educate staff about common cyber threats.
The problem of account takeovers, also know as “account hacking”, or “ATO” for short, tends to happen when users are careless about their login details.
While IT security goes a long way in patching flaws that could lead to ATOs, one of the best practices for prevention is to educate users about the value of their accounts.
You should regularly ensure that they do not reuse passwords, don’t share login details with anyone, and double-check that the communications they receive from you are genuine to avoid phishing attempts.
- Pro tip: You can use HaveIBeenPwned’s API to check if a password was compromised in a data breach.
5. Gather As Much Payment Data As Possible
Moving on to the problem of payments, you may already know how challenging it can be to win chargeback disputes, but it doesn’t have to be that way.
If you manage to gather as much information as possible about your customers – even those without an account on your site, you are putting the odds in your favor.
Here are examples of suspicious data you should be able to gather:
- Use of VPNs
- Brand new email addresses
- IP addresses pointing to locations far from the shipping destination
- etc.
The data is handy if you can look at it in real-time, but also if it’s logged in your system in case you need to dispute a chargeback request.
6. Verify Identities Without Adding Friction
Trusting people online is hard. This is true whether you’re dealing with customers, affiliates, or business partners.
The problem is that verifying IDs can add a tremendous of unwanted friction. Sure, you can deploy identity verification software to do it for you, but it still makes people pause to take a video selfie or find an ID document, which many consumers don’t appreciate.
The answer could be sourcing alternative data for customer due diligence. It’s all about looking at the right signals to ensure you’re dealing with the right person, without directly asking the customer.
Instead, you are examining their hardware and software setup, their email address, their IP address, phone number, bank card.
Here’s what to check for:
- A phone number pointing to a virtual SIM card could be bad news.
- Has this email address been used to register for any social media or online accounts? If not, this is highly suspicious.
- Card BINs from prepaid cards carry more risk. What type of card is being used?
- Devices with emulators, VPNs, or Tor usage can also point to someone hiding their true identity.
Some of these signals show surprisingly accurate results when it comes to identifying good users versus fraudsters.
Social media lookups, for instance, return fantastic real-time results that will flag email accounts hastily created for the purpose of defrauding your company.
7. Deploy Fraud Prevention Software
So, you’ve gone this far down the list and asked yourself: But how do I do that?
The answer is fraud prevention software. Sure, you could manually perform all the verification steps mentioned above, but if you want to work at scale, it makes much more sense to automate.
Fraud detection software, however, comes in many shapes and sizes. Some specialize in compliance while others are tailored for chargeback disputes, and more.
The key is to ensure you have the right tools at your disposal for your needs – and that they give you enough flexibility to evolve with your business as it grows.
- Pro tip: Check out SEON’s comparison of the best fraud detection software providers.
8. Look Out For New Compliance Requirements
Compliance and regulations are often seen as hoops companies have to jump through.
However, when authorities and regulators create these obstacles, you know that it’s because fraudsters and criminals aren’t far behind.
To ensure you don’t face litigation, fines, and negative press due to compliance issues, you simply have to stay ahead of the curve by noticing regulatory changes in other verticals.
For instance, Neobanks, iGaming, and other high-risk industries simply cannot afford to stay behind when it comes to understanding and meeting new regulations.
9. Use Dynamic Friction
Dynamic friction is a process that allows you to ask extra security questions when, and only when, you’re dealing with users you are not certain about.
Meanwhile, good users can perform their actions without extra verification, and high-risk users are immediately blocked.
The advantage of this strategy is that you don’t slow things down for the vast majority of legitimate customers.
It’s only if you have reasonable doubt that you will ask for an extra piece of ID, OTP verification or a CAPTCHA, for instance.
How do you calculate risk in order to implement this traffic-lights system? With risk scores. Put simply, it’s about feeding data through software that lets you decide if something is risky or not.
- Pro tip: Read about the basics of fraud risk scoring to make the most of a dynamic friction system.
10. Leverage Machine Learning
Last but not least, it’s time to bring out the big guns: artificial intelligence. Specifically, you want a machine learning system that is able to:
- Sift through huge amounts of business data
- Label good vs bad user actions
- Output suggestions to establish patterns
- Allow you to understand its decisions
Here’s an example from an online company selling footwear. They fed their fraudulent transaction data to the algorithm, and received back an interesting finding:
Purchases of size eight shoes tended to have a higher likelihood of resulting in chargebacks. The reason turned out to be that it’s one of the easiest shoe sizes to resell, which makes it attractive to fraudsters.
Knowing this information allows you to set up this shoe size for a little more scrutiny, if you prefer.
Perhaps an eagle-eyed fraud analyst would have spotted the pattern, but what’s interesting is that an AI system was able to identify and draw your attention to this pattern: size eight shoe purchases = elevated risk.
You could leverage the same power to draw connections and identify underlying patterns in your own online business.
- Pro tip: Consider the differences between blackbox machine learning and whitebox machine learning to find a system that meets your needs.
As the world moves into 2023, cyber security will need more attention as there’s going to be plenty of challenges to deal with, but things aregenerally moving in the right direction.
Threat’s only become more significant as we continue to transform digitally, but the fact that cyber security awareness is rising shows a good sign for the future.
We encourage you to keep on improving your cyber security through 2023 and beyond.









Charlie Bradford
March 5, 2024Your article on 10 anti-fraud measures is a valuable resource for businesses seeking to secure their operations and protect their customers. The inclusion of fraud prevention resources adds depth to the discussion, offering businesses a comprehensive guide to bolster their defenses against potential threats. This article serves as a practical and informative resource for businesses looking to implement robust anti-fraud measures.