These Cybersecurity Flaws Are Hackers Top Target, Patch Now
Cybersecurity researchers detail some of the security flaws that are most associated with attacks in recent times.

One of the most popular security vulnerabilities among cyber criminals during the past few months is a software security flawin Microsoft Office, CVE-2017-11882, first disclosed in 2017.
These flaws continue to be exploited because, despite a longstanding available security update, many businesses still haven’t applied it.
According to analysis by cybersecurity researchers at Digital Shadows,CVE-2017-11882 is the most commonly discussed vulnerability among cyber criminals on underground forums over the last three months,
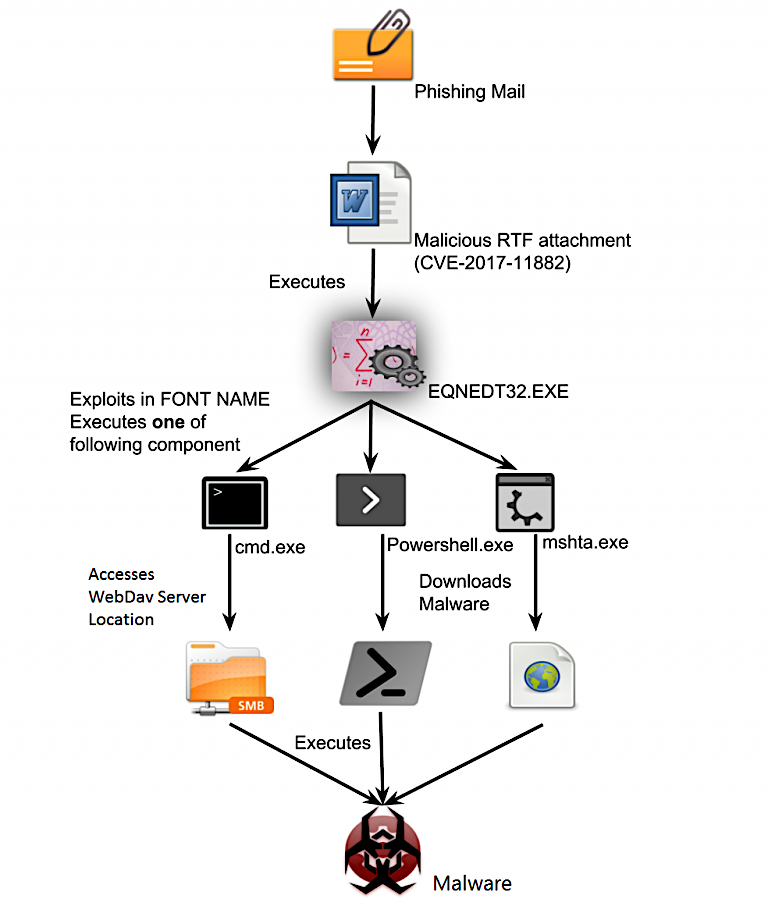
When exploited successfully, this vulnerability allows cyber criminals to execute remote code on a vulnerable Windows system, providing a way for attackers to drop malware secretly onto the machine.
Malware delivered in attacks exploiting CVE-2017-11882 includes Formbook, which secretly provides attackers with remote access capabilities, keystroke logging, and the ability to take screenshots.
Putting victims at risk of stolen usernames and passwords.
The vulnerability is also associated with the delivery of Redline, malware that steals usernames, passwords, credit card details and the contents of cryptocurrency wallets, along with the contents of chat logs.
Attacks looking to exploit CVE-2017-11882 often begin with phishing emails designed to lure victims into opening malicious documents, which trigger the bug.
Although a security patch for CVE-2017-11882 has been available for several years, the vulnerability is still prevalent enough to be commonly exploited by cyber criminals.
These older technologies are still in use by many organizations due to certain dependencies or preferences.
However, it’s these old legacy systems that cause these older vulnerabilities to live on and remain actively exploited years later.
The second most popular vulnerability during the reporting period was Follina (CVE-2022-30190), a high-severity zero-day vulnerability in Microsoft Word, which emerged earlier year.
Follina allows attackers to execute remote code and deploy malware to gain access to systems.
It has been actively exploited by state-backed hacking groups and cyber-criminal gangs. A patch is available to fix this vulnerability.
The third most popular vulnerability is CVE-2022-2294, a zero-day vulnerability in Google Chrome, first disclosed and patched in July.
However, many users are yet to apply the security update, so it remains a popular attack method for targeting Google Chrome users.
While regularly applying security updates for all manner of software across an enterprise network can be challenging, this is one of the best things businesses can do to help protect their network.
This helps prevent users from falling victim to cyberattacks, particularly when patching some of the most commonly exploited vulnerabilities.
“Organizations should employ a risk-based approach to their vulnerability and patch management processes. Not all critical vulnerabilities end up being exploited in the wild.”
“Vulnerability Intelligence can help provide valuable context to enable organizations to make informed, risk-based decisions,” said Hoffman.








